Shamoon malware (aka distrack) popularly known for its cyber emissary capabilities has re-surfaced. It’s back with an even more improved arsenal of taking down virtual machines. Just for a little sneek peek into what shamoon can do, shamoon has the ability to spread on local network. It can send a curated collection of relevant data or files from targeted locations on a computer to the attacker prior to deleting them. Also, shamoon can be capable of overwriting the MBR is rendering your machine aloof.
Shamoon was initialy spotted in 2012 when it was used to attack Saudi Aramco an oil company based in Saudi Arabia. It affected 35000 machines and it took almost a week to get the machines up and running again. Just in November 2016, a new exemplification of shamoon malware dubbed shamoon 2 was witnessed. It was employed to attack another Saudi Arabia based firm and was set to wipe their systems on November 17th.
Similarly, a second shamoon 2 occurrence was spotted in November by security researchers at Palo Alto networks and it was as well targeted in Saudi Arabia. Significantly, the second shamoon 2 malware contained hardcoded account credentials related to the victim organization as noted by the researchers and this was a behavior that hadn’t been observed in previous shamoon 2 occurence.
Given by the fact that the user credentials comply with the windows password complexity requirements, its then valid for the researchers to assume the existence of an unknown attack similar to the November 17th used to capture the usernames and passwords for the latest attack.
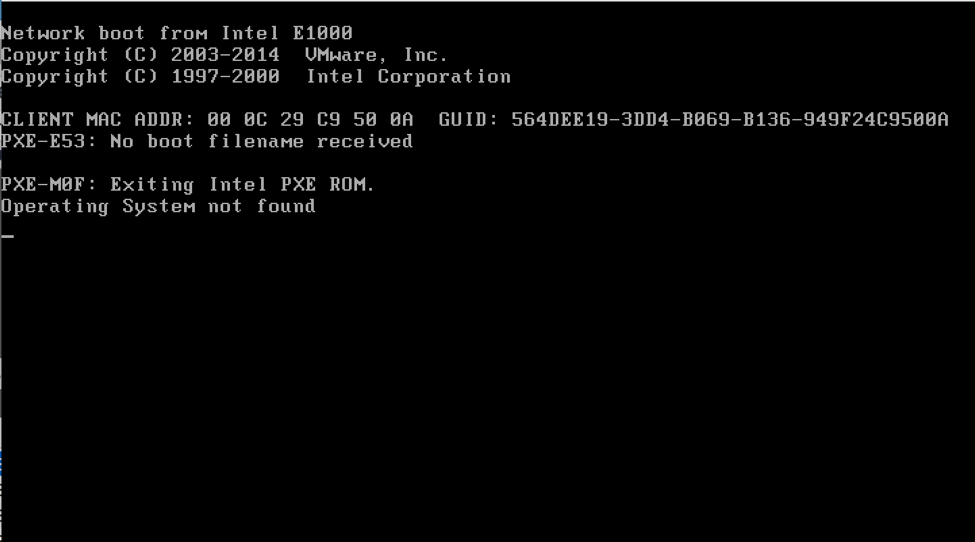
The updated shamoon also includes the administrator account user credentials. These are a part of the official documentation for Huawei’s desktop visualization products, like FusionCloud used to create a virtual desktop infrastructure (VDI). Such virtual systems are known to provide protection against malware like shamoon by aiding virtual desktop interface snapshots, backups made before the machine is wiped.
The credentials might have been used by the target organization to set up their Huawei VDI systems. The attackers most definitely included them to increase the intensity of the attack by disabling the virtual machine’s protection. However, It’s quite hard to figure out if the attackers initiated a previous attack to get hold of the credentials or these were only helping hands in making password guesses.
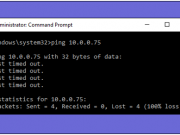
More so, the researchers are incognizant of the medium used to spread the malware that had been scheduled to wipe the systems on November 29th at 1:30 am Saudi Arabia local time. At such time, it’s barely possible that perhaps staff members were present in organization premises therefore increasing the revelation time and maneuvering for any possible remedies.