Spy Applications are becoming more of a household name today. With countless parents, spouses and businesses turning to their services to keep an eye on their loved ones and assets, there is no shortage of application available for those looking to purchase one as well. With the increase in their number and the lack of proper information present on the topic, most people do not really know what to look for when they are buying spy software. Thus, we are here to help you out. Following are a few key features that any good spy software must be equipped with at any cost.
- Keylogging
“Keylogging” is one of the very unique yet very important features that any good spy software must have. Keylogging essentially keeps a record or rather a log of every single word a user working on the target device uses. It can be anything, from keeping a record of the texts send to the keywords punched into a web browser to look something, keylogging keep tracks of it all.
Keylogging is a great tool for parents who want to keep an eye on what their children are looking for online and then to restrict their internet usage if they are wandering over to the website dealing with pornographic data. The same goes for employer who wants to avoid a potential legal nightmare by keeping a log of their employees’ internet browsing sessions and emails.
- Tap and Listen Live to Calls
This rather unique feature, though very useful, is hard to find in spy applications other than TheOneSpy. This feature allows into the calls sent or received by a used on the target device in real time and the chance to listen in to their conversation instead of having to do with a mere log that tell you how long the call lasted and how frequently does a certain person calls the target phone or receives the calls. This way, you are also able to discern if the user of the target device is guilty or not.
- Bugging
Thanks to movies and serials that deal with spy agencies like James Bond and The Man from UNCLE, every single person on the planet knows what “bugging” is. For those who don’t know what this is, bugging is the act of putting a tracker on the target device to track its location using the spy software and GPS too at time. Still, most people seem to think that bugging is only limited to spy movies. Now that is not true! Spy Applications utilize the same techniques and software as intelligence agencies do, (although it is not as sophisticated) to track missing people and lost devices. This way, people can keep track of their children and employees by tracking the electronic devices lend to them. Additionally, one can also listen into or see what is going on around the target device by turning on the camera or microphone remotely.
- Access to Gallery, Call and Text Logs
Any good spy software will always give you full access to the target devices’ calls, texts, emails, IMs, etc. i.e. you have complete and unadulterated access to the activities of the target device. You can also have a look at and browse through the target device’s internet history at your leisure. You will not only be able to keep an eye and monitor the user of the target device but also use the target device as if it is your own without having physical access to it.
- Remote Access
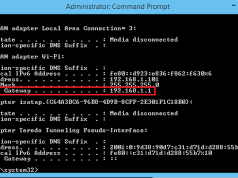
“Remote Access” is the technology that is responsible for the conception and popularity of the spy software. Remote access allows you to access the target device without having physical access to the device around the clock. It gives you regular alerts about certain activities as well as allow you to access the servers of the spy applications from anywhere in the world and look through the logs and other recorded data saved up on the servers for you to access from, anytime, anywhere.